Subnetting
Subnetting is the practice of dividing a network into two or more smaller networks. It increases routing efficiency, enhances the security of the network and reduces the size of the broadcast domain.
Consider the following example:
In the picture above we have one huge network: 10.0.0.0/24. All hosts on the network are in the same subnet, which has the following disadvantages:
organizational problems – in a large networks, different departments are usually grouped into different subnets. For example, you can group all devices from the Accounting department in the same subnet and then give access to sensitive financial data only to hosts from that subnet.
network security – each device can reach any other device on the network, which can present security problems. For example, a server containing sensitive information shouldn’t be in the same network as user’s workstations.
a single broadcast domain – all hosts are in the same broadcast domain. A broadcast sent by any device on the network will be processed by all hosts, creating lots of unnecessary traffic.
Subnet mask
An IP address is divided into two parts: network and host parts. For example, an IP class A address consists of 8 bits identifying the network and 24 bits identifying the host. This is because the default subnet mask for a class A IP address is 8 bits long. (or, written in dotted decimal notation, 255.0.0.0). What does it mean? Well, like an IP address, a subnet mask also consists of 32 bits. Computers use it to determine the network part and the host part of an address. The 1s in the subnet mask represent a network part, the 0s a host part.
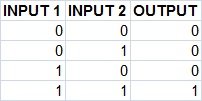
Computers works only with bits. The math used to determine a network range is binary AND.
Let’s say that we have the IP address of 10.0.0.1 with the default subnet mask of 8 bits (255.0.0.0).
First, we need to convert the IP address to binary:
IP address: 10.0.0.1 = 00001010.00000000.00000000.00000001
Subnet mask 255.0.0.0 = 11111111.00000000.00000000.0000000
Computers then use the AND operation to determine the network number:
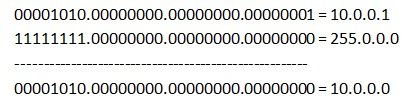
The computer can then determine the size of the network. Only IP addresses that begins with 10 will be in the same network. So, in this case, the range of addresses in this network is 10.0.0.0 – 10.255.255.255.
NOTE
A subnet mask must always be a series of 1s followed by a series of 0s.
DEFAULT subnet mask
By now you should have some idea what the subnet mask does and how it's used to partition a network. What you need to keep in mind is that each Class has its DEFAULT subnet mask, which we can change to suit our needs. I have already mentioned this in the previous page, but we need to look into it in a bit more detail.

This is really a good source of information, I will often follow it to know more information and expand my knowledge, I think everyone should know it, thanks Best python list comprehension service provider
ReplyDeleteNetworking Projects for Final Year , Subnetting is the practice of dividing a single physical network into multiple smaller, logical sub-networks, or subnets. Every device on a network has an IP address, but without subnetting, a large network would become inefficient and congested due to excessive "broadcast traffic"—messages sent to every device simultaneously. To manage this, a Default Mask is used based on the address class ($Class A, B, or C$). For instance, a Class C network traditionally uses a default mask of $255.255.255.0$, indicating that the first three octets identify the network and the last octet identifies the specific host.Customizing with the Subnet MaskA Subnet Mask is a 32-bit number that "masks" an IP address to distinguish which portion belongs to the network and which belongs to the host. While a default mask follows standard class boundaries, a custom subnet mask allows administrators to "borrow" bits from the host portion to create more networks. Network Security Projects for Final Year
DeleteThis process is essential for security and performance, as it isolates groups of computers from one another. By calculating the mask (often seen in CIDR notation like $/24$ or $/26$), an engineer can precisely determine the number of available hosts and subnets, ensuring that IP addresses are not wasted in smaller office environments or large data centers.
This is really a good source of information, I will often follow it to know more information and expand my knowledge, I think everyone should know it, thanks Best remote it support for small business service provider.
ReplyDeleteI generally want quality content and this thing I found in your article. It is beneficial and significant for us. Keep sharing these kinds of articles, Thank you.spunlace manufacturers in india
ReplyDelete